
Exploring CWE-329 Generation of Predictable IV with CBC Mode
Introduction
The OWASP Top Ten list provides in-depth information about the most common security issues facing web applications. Number two on the list is A02:2021 – Cryptographic Failures, which covers a wide range of common mistakes.
One of these cryptographic failures is CWE 329, which discusses the generation of a predictable IV when using CBC mode for encryption. This failure to properly initialize cryptographic algorithms can cause leaks and break data confidentiality.
How CBC Mode Works
Block ciphers, such as the Advanced Encryption Standard (AES), get their names from the fact that they encrypt data in fixed-size blocks. For example, AES has a block size of 128 bits. Block cipher modes of operation (MOO), such as cipher block chaining (CBC) mode, enable the encryption of plaintexts that are longer than a cipher’s block length. They describe the way in which each block of encryption/decryption relates to the next.
The operation of CBC mode for data encryption and decryption is shown in the image below. Before passing through an encryption algorithm (AES, etc.), the plaintext is exclusive-ored (XORed) with either an initialization vector (IV) — in the case of the first block — or the previous block’s ciphertext. In decryption, this XOR is performed after passing a block’s ciphertext through the decryption algorithm.
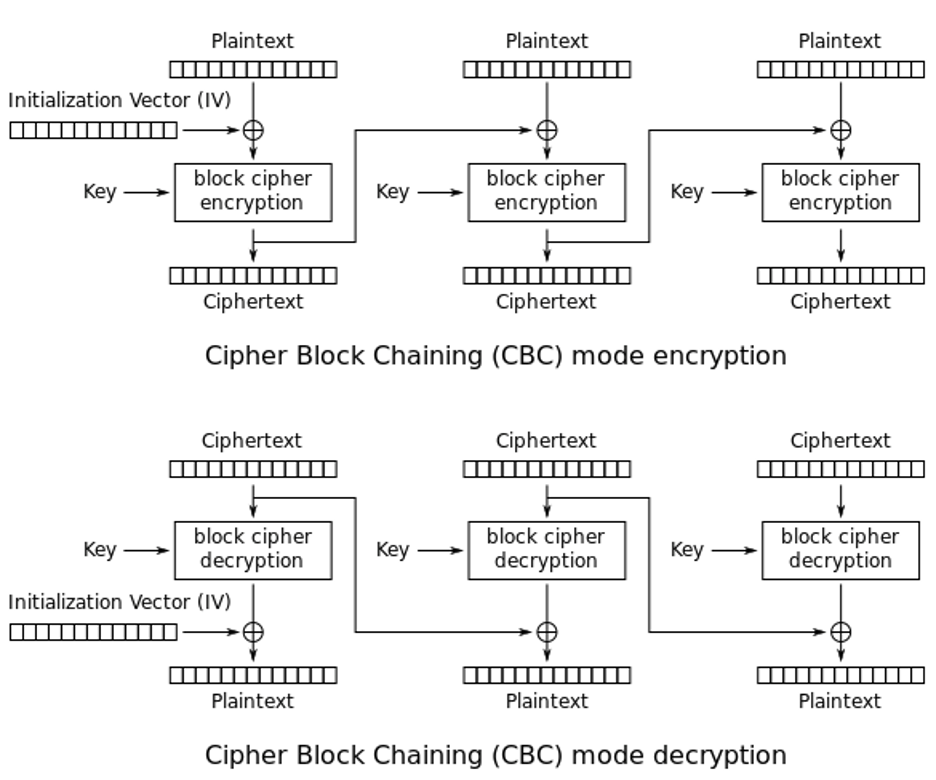
Different block cipher MOOs offer various benefits and levels of security. One of the benefits of CBC mode is that it allows decryption to be parallelized. The IV and ciphertext of each block are known in advance, so there is no need to wait for the decryption of block 0 to decrypt blocks 1, 2, etc.
Where CBC Mode Can Go Wrong
The IV used in the first block of encryption in CBC mode is not a secret value. It’s commonly sent along the public channel from the message sender to the recipient before the first block of encrypted data is transmitted.
Communications between two parties may use the same secret key for encrypting multiple chunks of data. Encrypting the same data with the same key produces the same ciphertext, which reveals information to an attacker. The IV helps to protect against this since changing the input to the first block changes its ciphertext, and these changes cascade through all encrypted blocks.
For this reason, it is important that the IV be unique and unpredictable for each communications session. Using the same IV for multiple sessions means that encrypting the same data will produce the same ciphertext. Even using a unique but predictable IV can break encryption security for chosen plaintext attacks.
While this may not reveal the contents of the message to an eavesdropper, it could leak valuable information. For example, an attacker that has observed that Alice sending message X to Bob causes Bob to take action Y knows what to expect if message X is sent again. Additionally, the fact that messages are not unique creates the potential for replay attacks where an eavesdropper sends message X without knowing its contents to trigger action Y.
Case Study: Spring Security
EnroCrypt is an encryption and hashing module for Python. In 2021, CVE-2021-39182 disclosed that the In 2020, a vulnerability was discovered in the CBC Mode Handler of Spring Security. The vulnerability potentially exposed data encrypted using the vulnerable code and is tracked as CVE-2020-5408.
The vulnerability dealt with the initialization of CBC mode in the queryable text encryptor. The code used a null initialization vector for encryption, meaning that encryption of the same data with the same key would produce the same ciphertext. This left the protocol potentially vulnerable to a dictionary attack where an attacker could determine the plaintext that produced a given ciphertext by making guesses and testing to see if they encrypted to the correct value.
Using CBC Mode Securely
CWE-329 is an example of a vulnerability that occurs when cryptography is implemented without a full understanding of the requirements of a cryptographic protocol. Cryptographic algorithms can be fragile, and even small changes, such as using a non-unique or predictable IV, can undermine their security.
Before using a cryptographic algorithm, it is important to understand its requirements and how to implement it properly. An even safer approach is to use a library that properly implements the cryptography for you, allowing safe encryption and decryption simply by calling an encrypt() or decrypt() function.
Up Next
To help build understanding of how cryptography can go wrong and how to fix it, we’ll continue to dive deep into prevention measures and most of the 29 CWEs related to OWASP’s A02:2021 – Cryptographic Failures vulnerability in a series of blogs. Each blog will describe the weakness, why it happens, a real-world case study, and recommended mitigations.
We’re very committed to improving the state of cryptography and data security by sharing knowledge and helping to correct common misconceptions about how cryptography works and how to use it properly. To keep up with this series and our other research and cryptography content, make sure to subscribe to our blog in the page footer below.
