Common Challenges with Key Management: Heterogeneity (Part 5 of 6)
Image credit: Photo by Jan Antonin Kolar on Unsplash
The Importance of Heterogeneity in Key Management Solutions
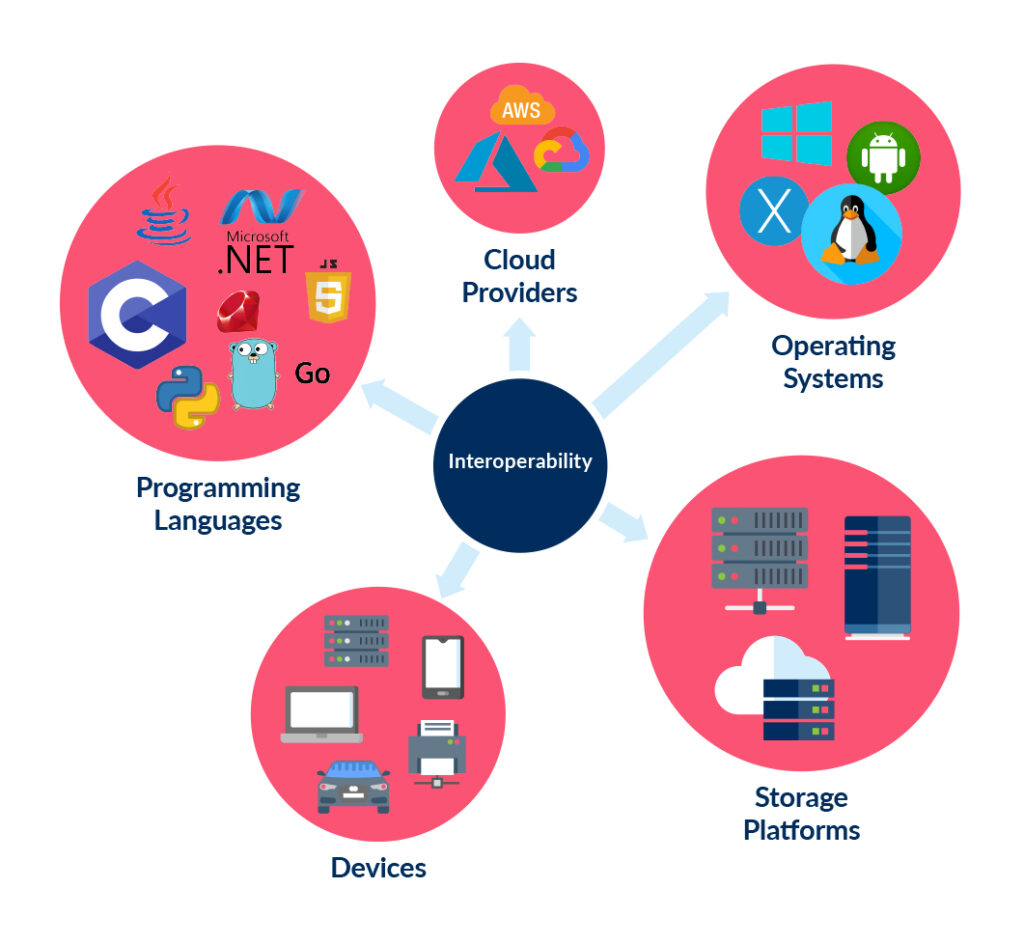
Organizations’ networks are growing steadily larger and more complex. Over time, the corporate network has expanded to include new types of endpoints, such as mobile and Internet of Things (IoT) devices, and new platforms and operating environments, like cloud based technology.
As the complexity of the enterprise network grows, so does the complexity of key management and authentication data in an effective and secure fashion. It is necessary to ensure that a key management system works for every type of device and software on the enterprise network and that it is consistently accessible to the organization’s users and applications.
Common Key Management Mistakes
Different systems may have different encryption and key requirements, and different departments within an organization may each have their own requirements and processes for key management. Attempting to navigate the growing complexity of key management drives a number of different mistakes that place the organization’s data and resource security at risk.
Inconsistent Policies and Enforcement
Ideally, an organization should have an enterprise-level security policy. This would outline procedures for appropriately classifying and protecting sensitive information across the entire organization.
However, heavily siloed organizations are more likely to have a number of different policies or methods for implementing and enforcing the overall security policy. As a result, the protection of sensitive information can be inconsistent across the organization, leaving potential weak spots for attackers to target.
These weak spots place both the department’s data and that of the entire organization at risk. The high level of interconnectedness of the modern enterprise network means that a foothold on one system may be leveraged to gain access to or view data on other systems.
Embedded/Hardcoded Keys
A complex and heterogeneous network creates an environment that typically results in poor key management practices. The sheer number of systems that a user or application may need to connect to can drive users and developers to provision and store encryption keys and authentication material in an insecure fashion.
For example, an application that requires access to a number of different resources and platforms needs to be able to easily access the required credentials. To simplify this process, developers will often embed the credentials within the code itself or in a configuration file deployed alongside it. This increases the probability that this sensitive information will be discovered by an attacker.
Ideally, these encryption keys and authentication data should be stored within a Hardware Security Module (HSM); however, this is not always feasible. To limit the potential impact of insecure key storage, all keys should be placed in a configuration file – not built into the application’s code itself – and should be set up to minimize the damage that could be caused if they are exposed (i.e. implementing least privilege and separation of duties). This makes it easier to detect and remediate any incidents caused by leaked keys.
Weak Keys/Passwords
Another common security error caused by the complexity of an organization’s environment is the use of weak or reused keys. The difficulty of remembering strong, unique keys for each environment can lead to the use of passwords based upon its purpose (like a database encryption password set to MySQL123! or P0stgr3) or the use of the same password for multiple platforms.
Both of these practices dramatically increase the probability that an attacker with access to the environment will be able to compromise these passwords and gain access to the target systems. Key management systems should be designed and implemented to make it easy for users and applications to access passwords and to enforce the use of strong, unique passwords for each resource.
Case Study: Gunnebo Group
In August 2020, Gunnebo Group, a Swedish firm specializing in physical security, suffered a ransomware attack and data breach. The company had stated that it successfully fought off the ransomware attack only to discover later that the attackers had stolen and publicly disclosed security blueprints of some of their clients. Many of these clients were heavily-guarded organizations like banks, nuclear facilities, and government agencies.
The source of the attack was traced back to a Remote Desktop Protocol (RDP) account set up by an employee to provide easy remote access to internal systems. This account had a password set to password01, which was easy to guess and provided attackers with direct access to the enterprise network.
How Ubiq Can Help with Key Management for Heterogeneous Networks
An effective key management system needs to be usable and effective across an organization’s entire network. This requires an encryption solution that can be applied consistently across the board and can be easily integrated into a wide range of programming languages.
Ubiq’s API-based developer platform offers an intuitive user interface for key management and libraries for common programming languages. To see how it can simplify and consolidate key management across your organization, check out this demo.
Read next: Common Challenges with Key Management: Governance (Part 6 of 6)