ECB vs. CBC – Pros and Cons of These Block Cipher Modes
Block cipher modes of operation are designed to allow encryption of data that is too long to fit in a single block of a block cipher. While a variety of block ciphers exist, this article will explore the pros and cons of the ECB and CBC block cipher modes of operation.
What is a Block Cipher Mode of Operation?
Cryptographic algorithms come in a few different forms. The major breakdown is between symmetric and asymmetric cryptography. Symmetric encryption uses the same secret key for both encryption and decryption, while asymmetric cryptography (also known as public key cryptography) uses a pair of related public and private keys.
Within the symmetric encryption category are block and stream ciphers. Block ciphers encrypt data in fixed-size blocks, while stream ciphers generate a stream of bits that are exclusive-ored with the plaintext to produce the ciphertext.
Block ciphers are designed to encrypt a single fixed-size chunk of data, which presents issues for plaintexts that are not exactly the correct length. Padding helps to solve the issue of undersized plaintexts, while block cipher modes of operation handle ones that span multiple blocks.
A block cipher mode of operation defines how the different blocks of a multi-block plaintext should be encrypted and decrypted. By agreeing on a block cipher mode of operation (like ECB or CBC mode), the sender and recipient of a message ensure that they do things the same way and that the data decrypts correctly.
How Does ECB Mode Work?
ECB mode is the simplest block cipher mode of operation in existence. Its approach to multi-block plaintexts is to treat each block of the plaintext separately.
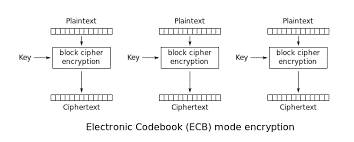
The image above shows how ECB mode works. Note that encryption/decryption of one block has no effect on the encryption/decryption of any other. While ECB is the simplest block cipher mode of operation to implement, it also has its issues.
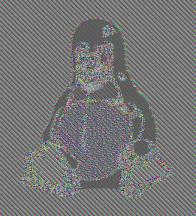
The image above shows the ciphertext resulting from the encryption of Tux, the Linux penguin, using ECB mode. Notice that the penguin is still visible even though the colors are distorted.
The reason that this happens is that, with ECB mode, encrypting identical plaintext blocks produces identical ciphertext blocks. In this case, each pixel is an independent block of plaintext containing the color of that pixel. Since, in this image, many of the pixels have the same color, those identical blocks encrypt to identical ciphertext blocks. As a result, Tux is still visible in the ciphertext.
While this is an extreme example, it demonstrates the limitations of ECB mode for data encryption. While ECB mode is faster, easier, and more parallelizable to implement, it leaks data about the underlying message being encrypted. Simply by observing the ciphertexts (which are public information), an eavesdropper can identify identical blocks and make guesses about the original plaintext.
How Does CBC Mode Work?
ECB mode’s issues arise from the fact that each block of the plaintext is encrypted completely independently. CBC mode eliminates this problem by carrying information from the encryption or decryption of one block to the next.
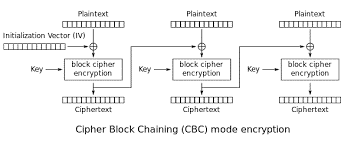
The image above shows how CBC mode works. For the encryption of the initial block, an IV is generated. This IV should be an unpredictable, unique value that is openly transmitted to the recipient. It is not a secret.
This IV is XORed with the plaintext before passing it to the encryption algorithm. The resulting ciphertext is then used to carry information to the encryption of the next block and so on.
This relationship between blocks helps to protect against identical plaintext blocks producing identical ciphertext blocks. Since each block of the plaintext is XORed with a different IV before encryption, it produces a unique ciphertext. This means that an attacker observing the string of ciphertexts can’t learn anything from the fact that two ciphertext blocks are identical.
A major advantage of CBC mode is that, while encryption must be performed sequentially, decryption can be parallelized. The first IV is a public value and all other blocks use a ciphertext as an IV, which are public. This can make decryption faster than other block cipher modes of operation.
Which One Should I Choose?
ECB and CBC are two of several different block cipher modes of operation. Each of these modes has its own pros and cons and selecting the right one depends on the needs of the project. For example, ECB and CBC mode provide confidentiality, while other modes, such as Galois Counter Mode (GCM), provide both confidentiality and integrity protection.
Between ECB and CBC mode, it is always better to choose CBC mode. As discussed above, ECB mode leaks information about the plaintext because identical plaintext blocks produce identical ciphertext blocks. A ciphertext should never leak any information about the plaintext used to create it, so ECB mode is insecure and should never be used.
CBC mode, on the other hand, is one of the most commonly used block cipher modes of operation due to its ease of implementation and support for parallelized decryption. However, when using CBC mode, it is essential that it be implemented correctly. Improperly implemented padding of ciphertexts can leave the system vulnerable to attacks like POODLE.
While CBC mode is better than ECB, GCM is better than both. In addition to providing strong confidentiality protections without the security issues known to exist in ECB and CBC mode, it also protects the integrity of the encrypted data by generating a message authentication code (MAC) as part of the encryption algorithm.
For this reason, the Ubiq platform uses the GCM block cipher mode of operation. For more information about painlessly integrating strong cryptography into your applications, check out the Ubiq cryptography libraries.
The feature image used in this Blog is attributed to Katka Pavlickova which was taken taken for FindByPlate | Two vintage Volkswagen beetles in the grass field