Bouncy Castle and the Impact of Cryptographic Vulnerabilities
Image credit: Photo by Pixabay
In December 2020, a vulnerability in the Bouncy Castle cryptographic library was publicly revealed. This vulnerability was discovered in October and fixed in November 2020. However, the nature of supply chain vulnerabilities means that many organizations remain vulnerable months later.
Inside the Bouncy Castle Vulnerability
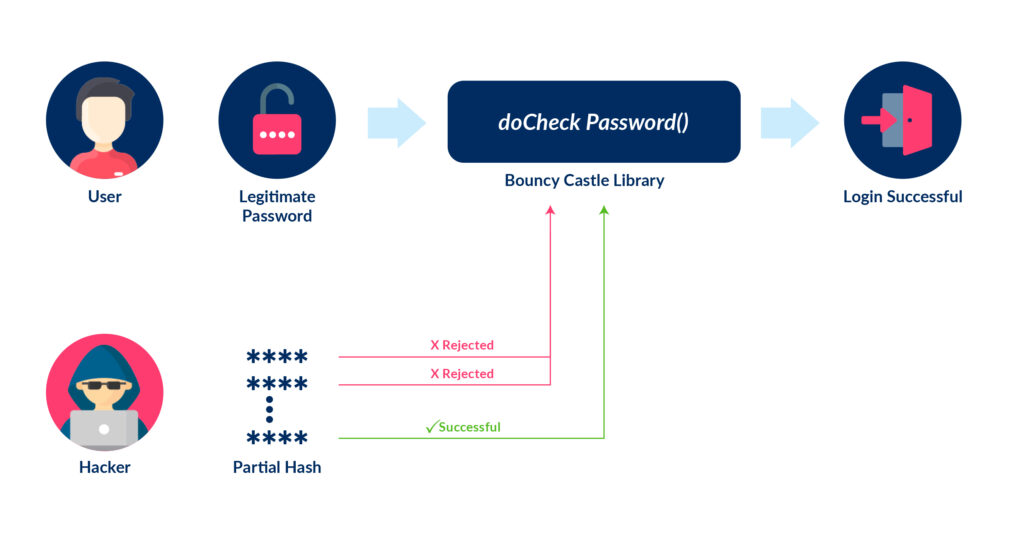
The Bouncy Castle vulnerability was a flaw in the implementation of the OpenBSDBcrypt.doCheckPassword() function. The purpose of this function is to compare the hash of a password submitted during user authentication with a hash stored by the system. If these hashes match, then the user authenticates successfully.
The vulnerable code in question is supposed to compare the values of the first 60 characters in the password hash (indices 0-59). If these characters match, then the password hashes are equals. This indicates that the submitted password is correct and authentication is successful.
Instead, the flawed code performs a search for bytes with values between 0 and 59 (inclusive) within the hashed version of the stored and submitted password. This means that two password hashes will be considered matching if one of two cases is true:
Both hashes do not contain the byte values 0-59
- In this scenario, the byte search will yield the non-index value -1 for both hashes. So, the isEqual value will be set to true since -1 is equal to -1.
- The bytes with values 0-59 are located at the same place in both password hashes
While it is improbable that either of these cases occurs, the probability is non-zero. When testing the vulnerability, the Synopsys security researchers that discovered the vulnerability found that, in 20% of cases, it took less than 1,000 attempts to find a password that matched a given hash. In the remaining cases, it is always possible to find a valid password, but it may take significantly longer.
Impacts of the Bouncy Castle Vulnerability
Bouncy Castle is a popular cryptography API for Java and C#/.Net. It is one of the most well-known and widely used cryptographic libraries in existence. According to NuGet, over 16 million copies of the library have been downloaded by .Net users alone.
The potential damage caused by the Bouncy Castle vulnerability is significant because the location of the vulnerability in the library (see diagram below). The doCheckPassword() function is commonly used to implement user authentication in web applications and similar services. This means that the vulnerability is publicly exposed and accessible to unauthenticated users (since it is part of the user authentication process).
The vulnerability was detected over two months ago and patched over a month ago at time of publication. However, it is highly likely that a high percentage of applications still use vulnerable versions of Bouncy Castle (versions 1.66 and below) and rely upon the vulnerable doCheckPassword() function for authentication. Since the vulnerability is contained within a cryptographic library, the developer of the application using it must be aware of the vulnerability and develop and push a software update containing the secure version of Bouncy Castle which is 1.67 [1] and above.
This makes the assumption that the developers in question regularly perform security testing and software composition analysis (SCA), where applications are scanned for the use of vulnerable libraries. However, 40% of organizations either insist that their applications do not contain open-source code or do not perform SCA. In these cases, it is unlikely that the Bouncy Castle vulnerability has already been detected or patched, potentially leaving the organization’s data and user accounts vulnerable to exploitation.
Minimizing Supply Chain Cryptographic Risk
As demonstrated by the recent SolarWinds hack, supply chain vulnerabilities can have a dramatic impact on an organization’s cybersecurity. When dealing with vulnerabilities embedded in third-party libraries, these issues can be difficult to detect and remediate if this responsibility lies with the organization.
The use of a Software as a Service (SaaS) encryption system can help to protect against and mitigate these types of vulnerabilities. By centralizing encryption functionality in a single system under the control of a third-party provider, an organization makes applying updates easier and the responsibility of its service provider. As a result, crucial updates, like the Bouncy Castle vulnerability patch will be applied more quickly and correctly.
To see the Ubiq Platform in action, check out this demo.