Authenticated Encryption: An Explainer
Image credit: Photo by Markus Spiske on Unsplash
Dozens of encryption terms and acronyms exist, which may be unknown even to those who have worked with encryption for a while. When individuals first start working with encryption, they often focus only on the simple task of encrypting and decrypting data. However, they may overlook other important concepts, such as Authenticated Encryption. Understanding the basics of encryption is a vital first step, but only grasping the basics is not enough. Encryption is not like other software development; a running program does not mean that the work is done. Although a developer may have encrypted the data to protect it from prying eyes, the systems or data may still be vulnerable to an attack.
In its simplest form, encryption is the process of securing some information and producing cipher text (see Figure 1.), which is ideally indistinguishable from random data. Encryption is a reversible process where the correct key is used to decrypt the cipher text and return the original information.
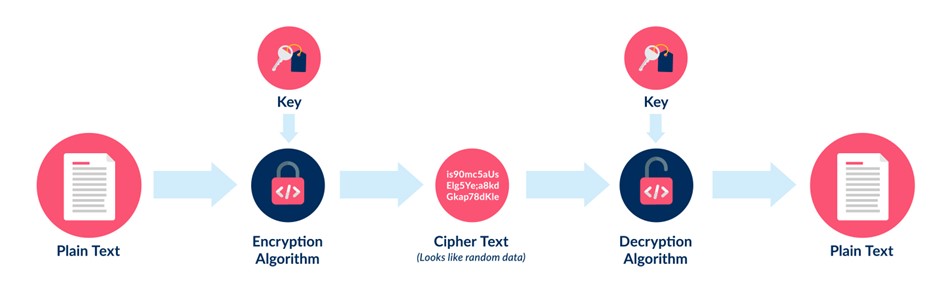
Figure 1 – Basic Encryption | Decryption
Encryption secures the data from prying eyes. However, many encryption algorithms will simply attempt to decrypt whatever cipher text it is provided. In other words, nothing verifies the integrity or authenticity of the cipher text to ensure it has not been altered. This lack of verification can lead to a number of problems.
For example (see Figure 2.), consider encrypting a bank’s wire transfer instructions containing data to transfer $100.00 from account A to account B. Many may believe that this is enough because an attacker would not be able to tell the amount of money or accounts involved in the transaction if the data is encrypted; however, if the bank chose an unauthenticated encryption algorithm, it could be in for a rude surprise. Because the cipher text and key are not verified, it may be possible for an attacker to change the cipher text in such a way that the decryption process does not realize the data has been altered and when the modified cipher text is decrypted, the wiring instructions would contain instructions to transfer $999.00 from account A to account C.
Again, with an unauthenticated encryption algorithm, an attacker could do this without being detected and without knowing the encryption key. While it seems like this should not be possible, certain encryption algorithms and modes are susceptible to certain attacks such as this.
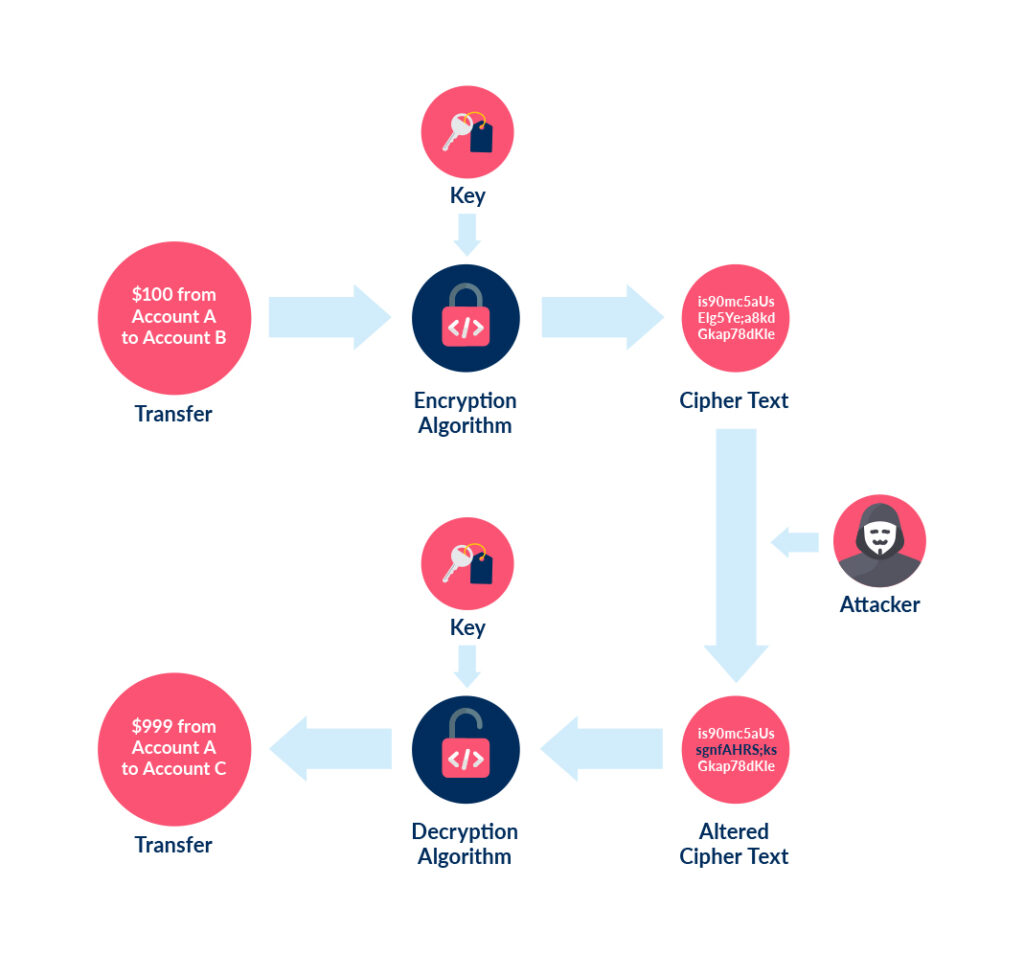
Figure 2 – Potential weakness of unauthenticated encryption
Similarly, some unauthenticated encryption algorithms will simply attempt to decrypt whatever data is presented with whatever key is provided. Such algorithms may be more susceptible to brute force attacks which can yield the encryption key or allow partial decryption of the cipher text.
This is where Authenticated Encryption comes in (see Figure 3). Several variations and approaches exist, but they are all different modes for ensuring the confidentiality and authenticity of the encrypted data. In general, the process creates a message authentication code (MAC), which is also commonly referred to as an Authentication Tag, that is used to verify the data’s authenticity.
There are three basic approaches to Authenticated Encryption using a MAC: Encrypt-then-MAC, Encrypt-and-MAC, MAC-then-Encrypt. As the names imply, the difference is when the MAC is created and what inputs are used to create the MAC. Figure 3 shows the basic flow for Encrypt-then-MAC which is regarded as more secure because the cipher text and MAC can be tested without decrypting any data. This means it can abort if it detects the key, cipher text, or authentication tag have been tampered or do not match. In the case of the wire transfer instructions above, the process working with the encrypted data would immediately recognize that an attacker had altered the data and reject the wire transfer instructions.
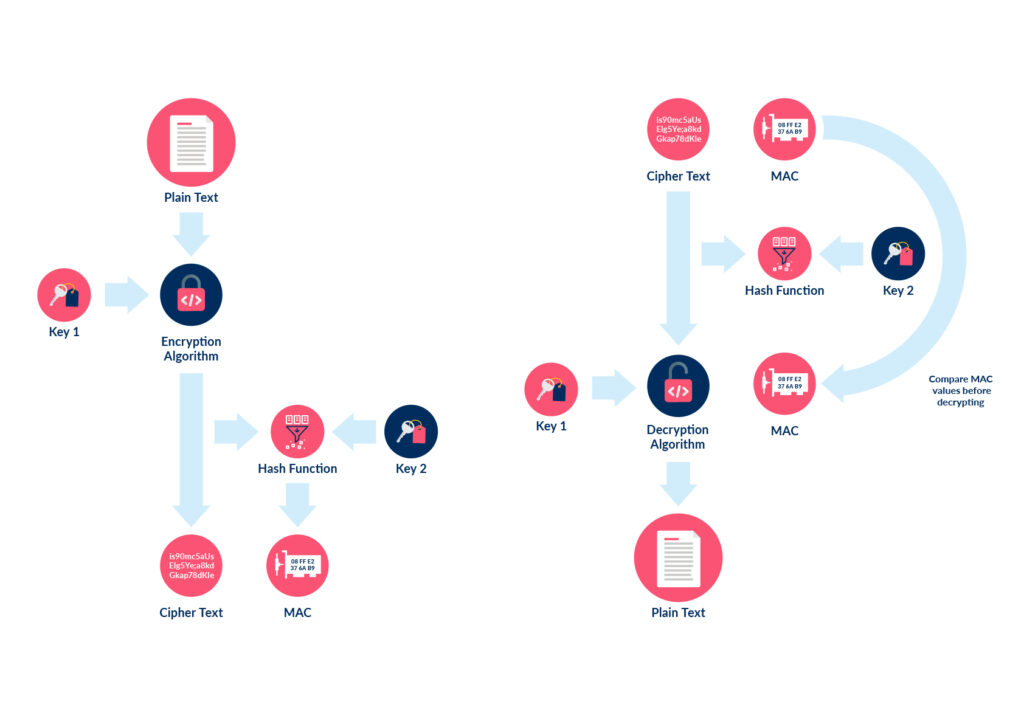
Figure 3 – Authenticated Encryption and Decryption
For reference, some common Authenticated Encryption modes are EAX, CCM, GCM, and Poly1305. Ubiq uses GCM by default because it is widely adopted, is faster than other modes, and uses the Encrypt-then-MAC approach.
Although this article focuses on the importance of Authenticated Encryption, dozens of other terms and concepts are also important. The Ubiq Platform’s APIs can simplify and improve an application’s data security and integrity by using a combination of Authenticated Encryption and other key concepts that we will examine in future posts. Ubiq also constantly monitors the latest research related to encryption algorithms, modes, and vulnerabilities, and it incorporates the newest information into the platform, ensuring the data remains as secure as possible.
To see the Ubiq Platform in action, check out this demo.
Setup is quick and easy
Ready to get started?
Create a FREE account instantly and start encrypting data or get in touch to discuss a custom package for your organization.
