Improving Cryptographic Security in Android Applications
Image credit: Photo by Stephen Frank on Unsplash
Cryptographic security is a challenge for many developers as cryptographic algorithms are often fragile. Even a small mistake in design or implementation makes them breakable, negating their security benefits. And because most developers have limited knowledge of cryptography, it’s no surprise that using it properly is a common problem.
A recent study by researchers at Columbia University demonstrated just how bad the problem is. The study analyzed the cryptographic security of 1,780 popular Android apps in the Google Play Store and revealed that many mobile developers are failing to properly protect sensitive data within their applications.
Inside the Cryptography Study
The researchers at Columbia University developed Crylogger, an automated tool for identifying insecure usage of cryptographic algorithms. The tool analyzes applications while they are running and flags any misuse of cryptography within the application as it occurs.
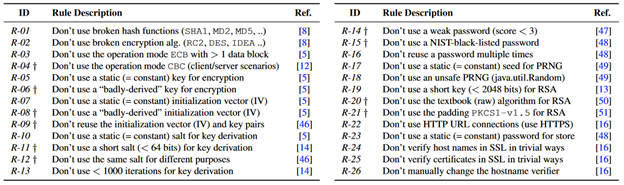
In this case, “misuse” is defined as making calls to cryptographic APIs that violate best practices, such as those defined by NIST and the IETF. The researchers defined 26 different cryptographic rules (shown below) that were extracted from 12 different standards and academic publications defining cryptographic best practices. These rules cover issues ranging from general bad security practices (like the use of a weak password) to misuse of algorithms or the use of broken cryptographic algorithms.
Android App Cryptography is Abysmal
The 1,780 Android apps chosen for this study were the most popular free applications in 33 different categories on the Google Play Store. Based on their analysis of these applications, the researchers determined that all of the apps studied violated at least one of the 26 cryptographic rules. However, some mistakes were more common than others. These include:
- Use of a weak pseudo-random number generator (PRNG): All but five of the studied apps used a weak PRNG to generate random values within their cryptographic implementations (secret keys, initialization vectors, nonces, etc.). This makes it easy for an attacker to guess the “random” value, potentially compromising the security of the encrypted data.
- Use of a broken hash function: Hash functions are designed to be collision-resistant, meaning it is difficult to find two inputs that produce the same hash output. Broken hash functions (like MD5 and SHA1) should be deprecated after collisions have been found. However, 1,764 of the 1,780 Android apps studied used a broken hash algorithm.
- Use of Cipher Block Chaining (CBC) mode for client-server communications: CBC mode is a block cipher mode of operation that defines how to encrypt and decrypt a plaintext that does not fit into a single block of a block cipher. CBC mode is considered insecure because its implementation is vulnerable to padding oracle attacks. Yet more than half (1,076) of the studied Android apps used this block cipher mode of operation.
While none of the remaining rules were violated by more than half of the studied Android apps, all of them were violated at least six times. This includes vulnerabilities that do not require any specialized cryptographic knowledge, such as the use of a hardcoded password (48 apps).
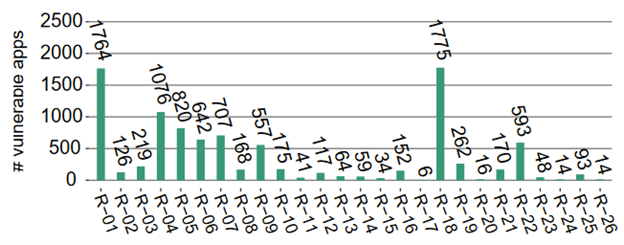
The table above taken from the Columbia University study shows the number of applications the researchers discovered violating each of the 26 rules studied. They also acknowledge that because Crylogger analyzes the code at runtime, there may have been additional issues that did not occur during the researchers’ test cases. A comparison with CryptoGuard, a commonly used static analysis tool for identifying cryptographic misuses, found that Crylogger identified vulnerabilities that CryptoGuard missed and vice versa.
In addition to the automated testing, the researchers also selected 28 apps (half that contained many vulnerabilities and half chosen randomly) and manually reverse engineered them. They discovered that half of the 28 apps were vulnerable to exploitation due to their weak use of cryptography and that some rules generated false positive detections, often when mistakes were made in “non-critical” parts of the application.
The Impacts of Poor Cryptography
The Columbia study of Android applications demonstrated that many developers struggle to properly implement cryptographic functionality within their apps. While some issues were caused by failing to follow common sense security practices (using weak and hardcoded passwords) others were derived from a failure to select the correct algorithms and functions to implement cryptographic functionality. The impact of even simple errors in cryptography can be significant.
- Weak encryption makes it easy for an attacker to decrypt data and access sensitive information.
- The use of weak passwords and encryption keys could allow an application or device to be compromised and used for further cyberattacks (DDoS attacks, etc.).
- A weak or broken authentication algorithm could enable an attacker to access other users’ accounts.
- Using the wrong encryption algorithm could reduce efficiency and increase overhead and costs.
- Marketing an application as “secure” when it contains broken cryptography can damage an organization’s public image (like the many issues with Zoom’s “end-to-end encryption”).
- Data protection regulations like CCPA and GDPR require proper protection of sensitive data. Poor cryptography could expose an organization to regulatory penalties and legal action.
This study demonstrated that many organizations are exposed to one or more of these potential threats. In order to protect their applications, data, customers and reputation, businesses need to find ways to help Android app developers use cryptography properly in their applications.
Taking the Complexity Out of Cryptography
Ubiq takes the complexity out of cryptography, making secure development faster, easier and more accessible for developers. Ubiq’s solutions are designed to take the guesswork and complexity out of cryptography. Instead of relying on the developer to correctly choose a secure algorithm or source of randomness, Ubiq’s cryptographic API simply exposes functions for securely performing encryption and decryption.
Behind the scenes, Ubiq implements the required cryptographic functionality based on accepted best practices and data protection regulations set by PCI DSS, GDPR, HIPAA and others. This includes the use of approved algorithms, key lengths, and the secure storage and management of encryption keys to provide additional protections against exposure.
Developers no longer need a deep knowledge of cryptography to build secure applications and businesses can accurately claim their Android applications use cryptographic workflows that follow security best practices. You can learn more about how the Ubiq Platform can work for your Android applications.
Setup is quick and easy
Ready to get started?
Create a FREE account instantly and start encrypting data or get in touch to discuss a custom package for your organization.